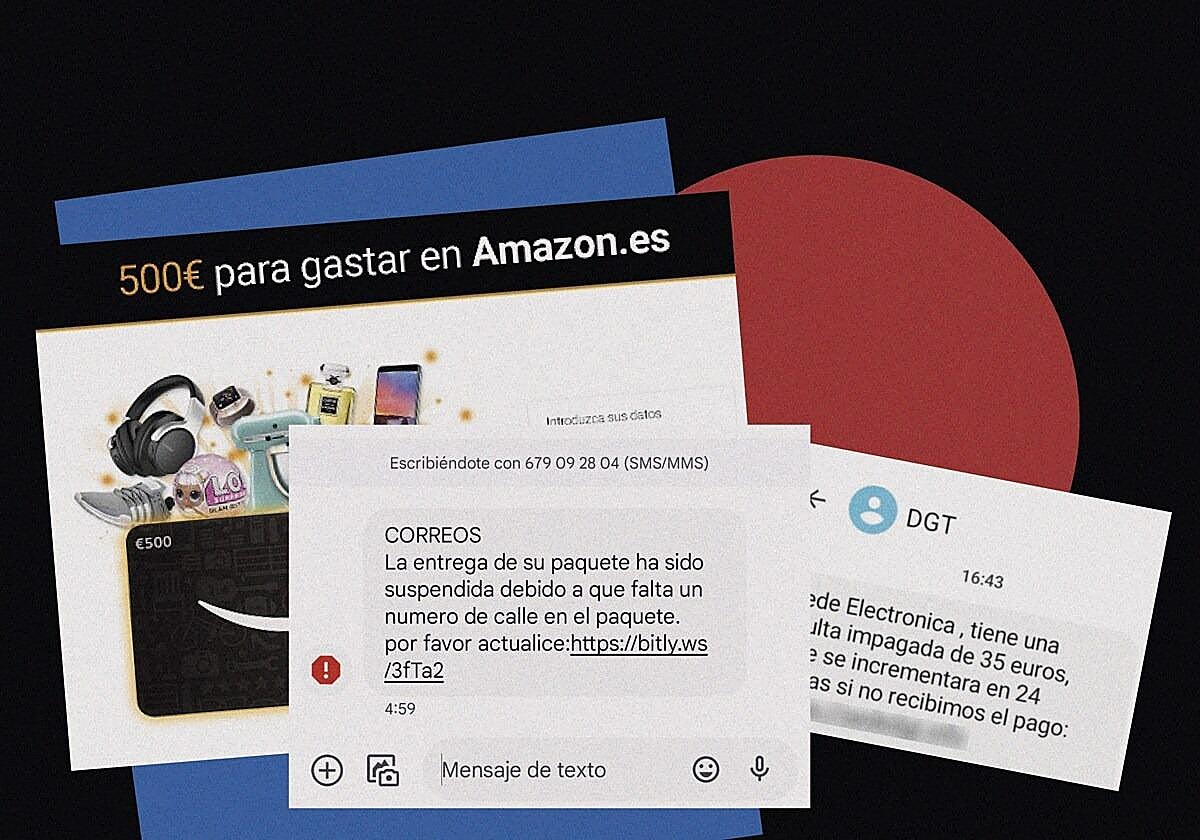
The post office, Netflix, a child in trouble, a fine... the most popular scams in circulation
Endesa, Amazon, Wallapop, the police or the job agency are also used as bait for massive phishing and smishing campaigns
Cybercriminals are constantly innovating and this is one of the reasons why fraud attempts continue to be successful, with new scams emerging almost every day. What are the scams that have been proliferating in cyberspace lately and how do you avoid falling for them? Here are twelve of the most typical:
1
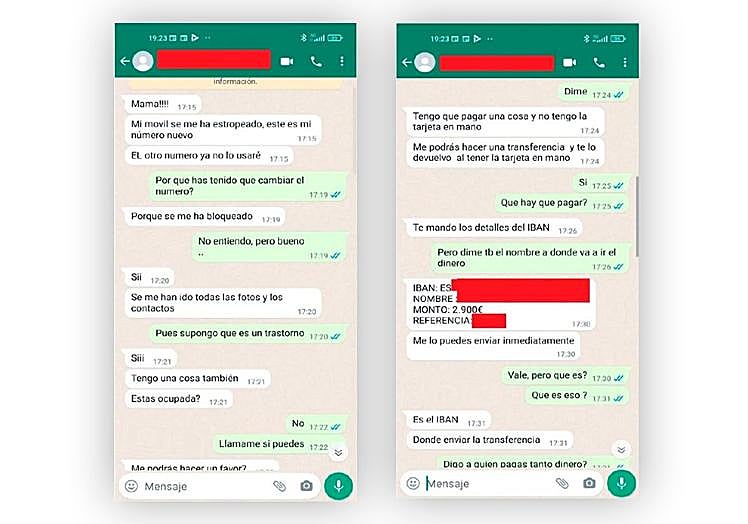
The child in trouble
Zoom
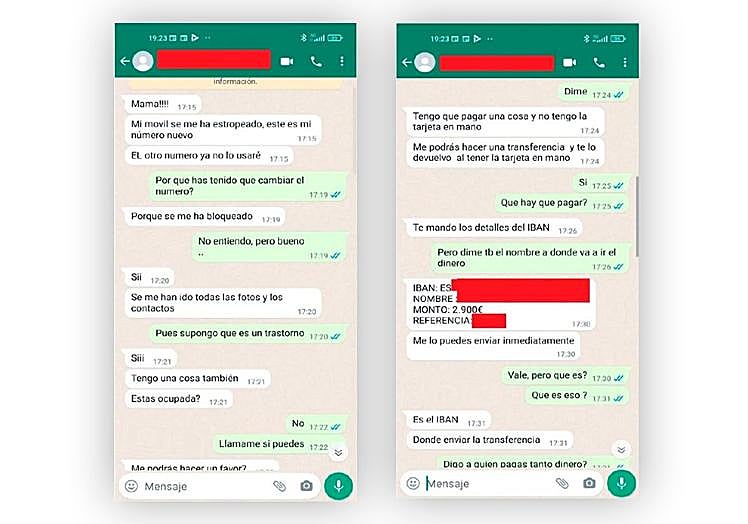
Last Christmas marked a real epidemic of this WhatsApp scam. The scam is carried out through a message in which the offender pretends to be the recipient's son or daughter, says that they have lost or had their mobile phone stolen and asks for a sum of money via a transfer to quickly solve a problem (e.g. to buy another mobile phone).
At the end of January, the National Police arrested 59 members of a criminal organisation allegedly dedicated to the 'child in distress' scams , which allegedly made a profit of more than 460,000 euros.
Within the organisation there were members who were dedicated to analysing social media of the possible children of the victims. When they found young people who were away from their place of residence, generally because they were studying outside Spain, they collected as much information as possible to make the conversation they would have with them more credible in order to carry out the scam.
Once they had collected all the information, they found a way to contact the parents of the young people and, after claiming to be in an emergency situation, they asked their relatives to provide them with money immediately in order to get out of a very complicated situation.
What should we do if we receive this message? First of all, stay calm and don't let yourself be carried away by the fear that your child is in trouble. The first thing to do is to call them on their real mobile phone. If they do not not answer, do not panic, as it is most likely that they cannot answer the phone at that moment. To find out for sure, you can ask a question that only your child can answer.
It is recommended, in any case, to report the telephone number from which you have been contacted to the police.
2
Netflix

Zoom

National cybersecurity institute Incibe recently reported a Netflix impersonation campaign in which, via an email sent to users, they are informed that their subscription to the service has been suspended or will be suspended imminently due to a problem with the bank charge for the renewal. In order to make the renewal effective, a link is provided to a fake website where the victim will find forms to enter their account credentials and personal and bank details.
"When clicking on the link provided, the user is redirected to a supposed Netflix login page, which uses on the company's corporate images and colours. An indicator that the page is not an official service is the use of a different URL from the original service," explains Incibe.
If we have entered our personal and banking information, cybercriminals will already be in possession of our data to use for future fraud or to commit cybercrime in our name.
3
The traffic fine

Zoom

A 'smishing' campaign (text messages or SMS with fraudulent purposes) has also recently been detected in which the identity of the Spanish directorate-general for traffic, DGT, is impersonated. These messages inform recipients that they have an unpaid fine, and invite them to pay via the link provided. In this way, cybercriminals obtain personal and bank details.
There are already clues in the text message that its origin is illegitimate, as it contains spelling mistakes. The user who clicks on the link provided in the text message will end up on a website with the DGT logo, where a final notification of an unpaid fine is made before the surcharge, communicating that the user has 24 hours to pay. Clicking on the "Pay the fine" button takes you to another screen where you are asked for personal information (surname, first name, date of birth, postal address, postcode, city, email, telephone number) and, once filled in, you are asked for credit card details (number, expiry date and CVV) to make the payment. If all these data are entered, cybercriminals will have them in their possession to use as they please.
4
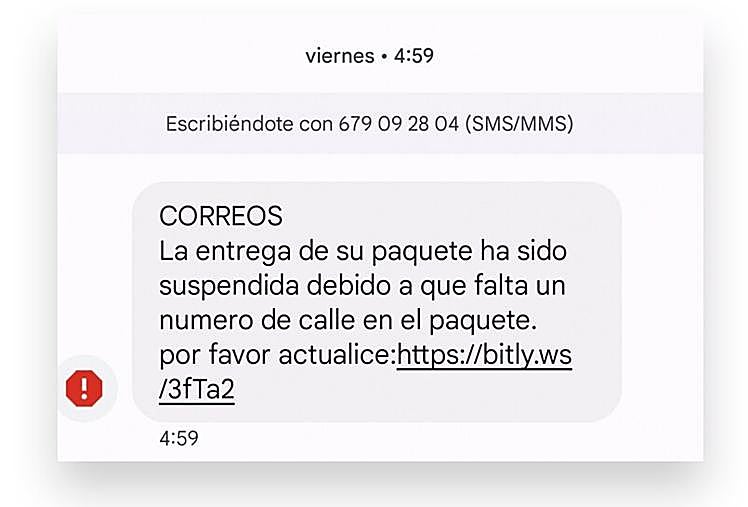
The undeliverable package
Zoom
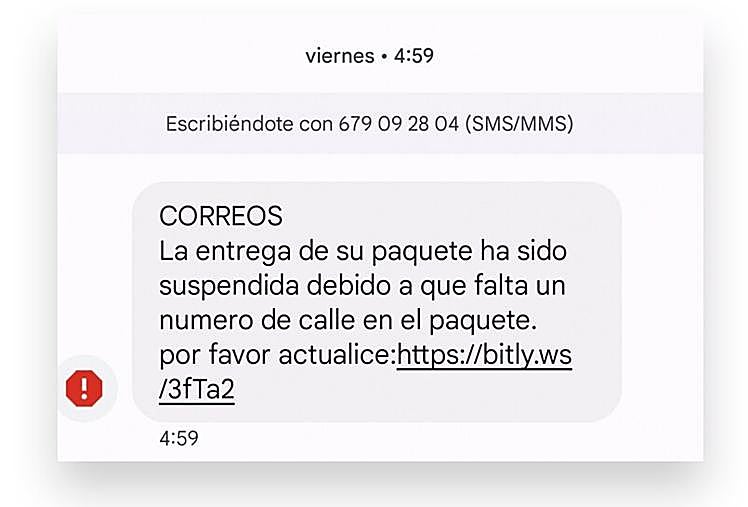
One of the most persistent cyber scams circulating via mobile phones and emails is the undeliverable parcel scam. The bait is an email or text message stating that there is a package that the post office cannot deliver because a payment for customs costs is due. The subject of the email is usually soemthing like "You have a package waiting to be delivered", although there are many variations. In these communications, grammatical and formatting errors have been detected, a clue that they are false.
In the case of the emails, the domain used in the email pretends to come from Correos, but it is not exactly the same as the legitimate one. In the email, the user is asked to buy a PIN code on the Paysafecard platform and send it to an address.
It has also been detected that this campaign uses SMS for a similar purpose, under the excuse of needing to confirm parcel delivery address details. "Your package has been put on hold due to a missing street number on the package. Please update the delivery information," many of these messages say. The URL will redirect to a site that mimics the Correos logo and warns that there is a deadline to receive the delivery and that we can pay a fee for them to make a new delivery attempt. The website redirects to a supposed payment gateway where bank details are requested.
Incibe reminds us that if there are doubts about the location of a package, you can access the official Correos website and check it with the tracking number. In addition, Correos has set up a email verifier to detect these frauds.
5
The job offer

Zoom

Specialists in cyber crime attached to the provincial police station of Malaga have warned of an increase in scams committed through a new modality that uses false job offers as a hook.
The scheme begins with the announcement of a job offer, which usually arrives via social media, although they also use instant messaging or websites where the user registers. Once the potential victim's attention has been caught, they contact them to establish the working conditions, offering varying amounts of money, ranging from 5 to 50 euros in exchange for watching videos, subscribing to content creation pages or clicking the 'Like' button on certain publications.
At the beginning, the worker begins to earn small amounts, commissions that encourage the victim to gain their trust. Once these small amounts have been earned, they ask for a deposit or transfer in exchange for instructions with greater profitability, at which point the scam is complete.
In addition, it has been found that in some cases, personal data has been requested to be used for other criminal purposes - financial fraud or identity theft - or the installation of malicious software on the victim's device.
6
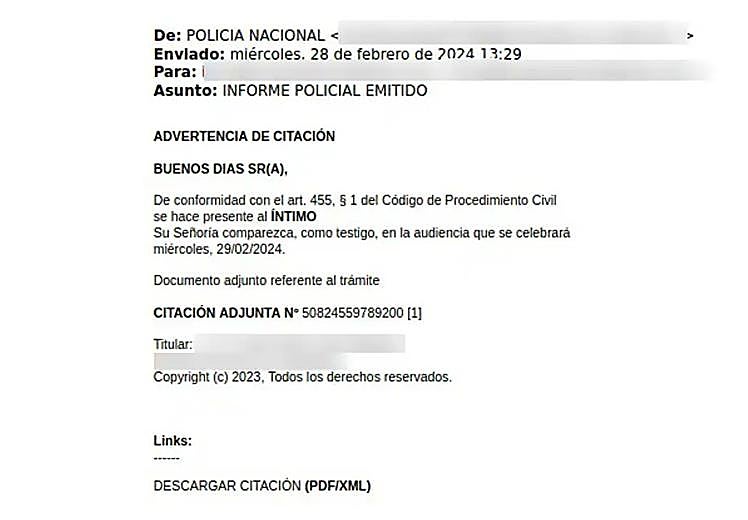
The police summons
Zoom
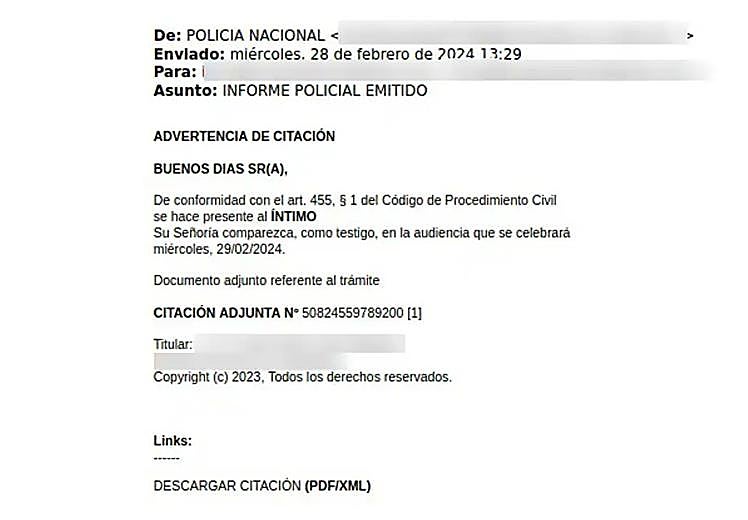
Incibe warns of a phishing campaign that impersonates the National Police in order to distribute malware (malicious software) through notifications that refer to a supposedly issued police report and a summons warning, requesting the person receiving the email to appear as a witness at a hearing to be held on a certain day.
To do this, the victim is provided with a link that supposedly contains the download of the summons, but in reality it contains a file with malicious content.
It should be borne in mind that the police will never contact citizens with this type of email. In addition, there are some indications that make one suspect that this is a fraudulent email: for example, the design is very simple, without any kind of official logo and the domains of these emails are not related to those used by the National Police.
7
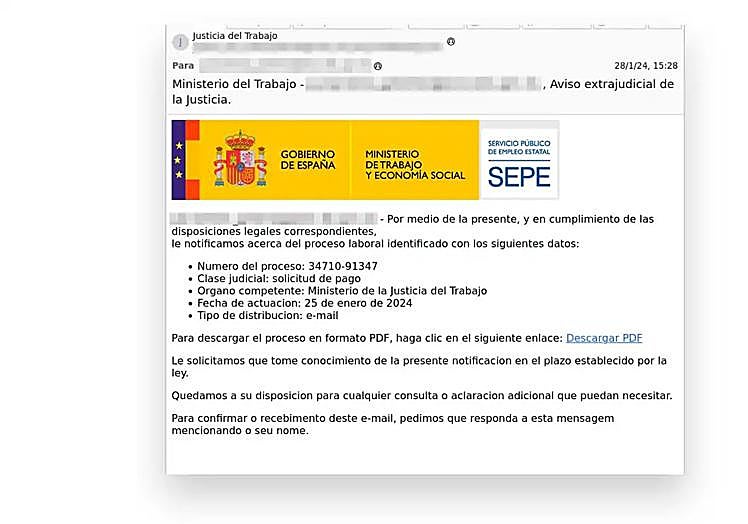
The job centre
Zoom
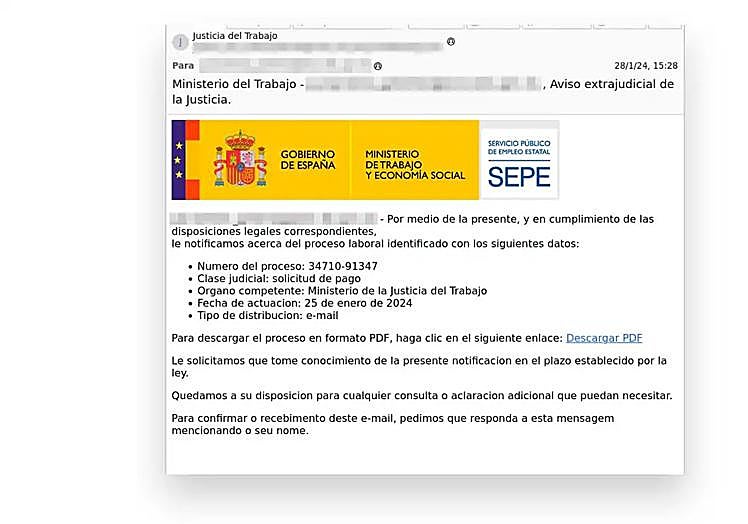
Another of the phishing campaigns detected lately in Spain is one that impersonates the SEPE (state employment service), using the sending of a notification as bait. The aim is for the user to download a file that supposedly contains documentation, but which in reality contains an executable file (EXE) with malicious code that infects the device.
The subject line detected for this type of attack is the following: "Ministerio del Trabajo – [recipient's email], Aviso extrajudicial de la Justicia."
The mail includes the logo of the ministry to which the SEPE belongs in an attempt to give veracity to the notification, but if we examine the body of the message, it indicates that the competent body is the Ministerio de Justicia del Trabajo, which does not exist.
8
Cloned online store
Zoom
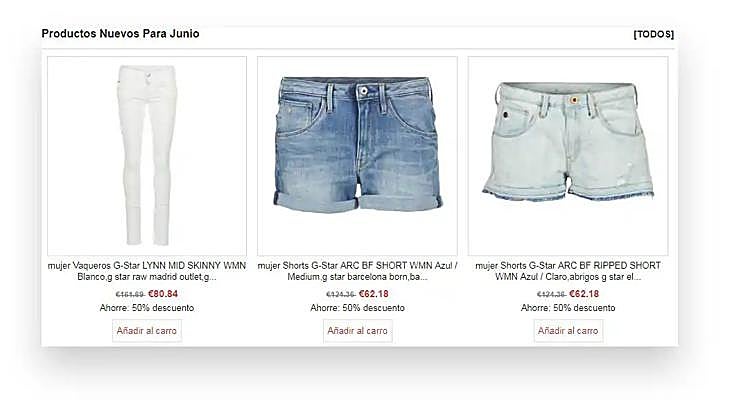
We can fall for a cyber scam by searching the internet, checking our social media or because a well-meaning friend passes us a link so that we can take advantage of an alleged bargain. Cloned shops are copies of the websites of well-known brands that supposedly offer the same products at heavily discounted prices. These pages proliferate in times of high commercial demand and, above all, discounts, such as Black Friday. If we fall for them and make a purchase, not only will we never receive the goods, but our credit card details will have ended up in the hands of cybercriminals.
Fraudsters copy the design and interface of legitimate shops. They use names very similar to those of the original brand, inserting or deleting a barely noticeable character, or registering the site under domains with '.shop' endings. In addition, they use SSL certificates to display the https protocol (the famous padlock), which is (wrongly) considered to be an indicator of a trusted site.
Incibe gives a series of tips on how to identify a fraudulent online shop:
-Be wary of flashy discounts.
-Look at the visuals: a poorly constructed, unattractive or typo-ridden website is a sign that it has been built in haste for these criminal purposes.
-Check the company's legal information: VAT number, company name or contact details.
-Click on the 'padlock' to check the certificate information and whether it matches the company it claims to be.
9
The bank

Zoom

There are many 'smishing' campaigns circulating that impersonate the identity of various banking institutions in Spain, such as ING, ABANCA, Banco Sabadell, Bankinter, Laboral Kutxa, BBVA, Banco Santander, Caja Sur, CaixaBank and Deutsche Bank. The victim is informed via SMS that there has been an unusual transaction in their account, for example, that a new device has been registered, that a large immediate transfer has been detected, that their card has been temporarily limited or that their account is going to be suspended. In order to resolve these situations, the user is told to click on the link provided in the text. This link will redirect them to a fraudulent website with the intention of obtaining their online banking access credentials.
"The messages try to give a sense of urgency so that the victim feels the need to respond immediately, and the reasons for these alarming messages tend to be of various types, among which we can find messages that include blocking accounts, processing loans and unauthorised charges," explained Incibe.
10
Wallapop

Zoom

Apps for buying and selling second-hand goods, such as Wallapop or Vinted, have their own list of scams and frauds. Through social engineering and phishing tactics, cybercriminals try to get hold of users' bank details, especially those new to these platforms.
The fraudster contacts the victim posing as a buyer. They talk to them, reach an agreement and, once they have reserved the product, they tell them that they cannot complete the transaction until they provide the email address with which they have registered. From there, the cybercriminal will send an email posing as the application itself (Wallapop or Vinted), indicating that an item for sale has been reserved and requesting that a button be clicked.
This is where phishing takes place, as the link leads to a website identical to Wallapop's, where the victim is asked for a series of data: email address, password and even credit card details, under the pretext that they are necessary to confirm the account. This is obviously a strategy to get hold of this data and use it fraudulently.
The moral of this type of fraud is the same as always: always be wary when someone asks for personal or bank details or asks you to continue trading outside the platform.
11
Amazon
Zoom
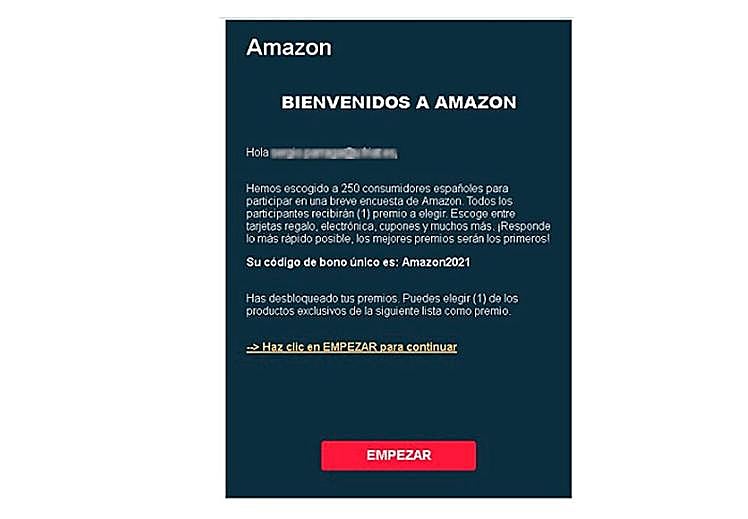
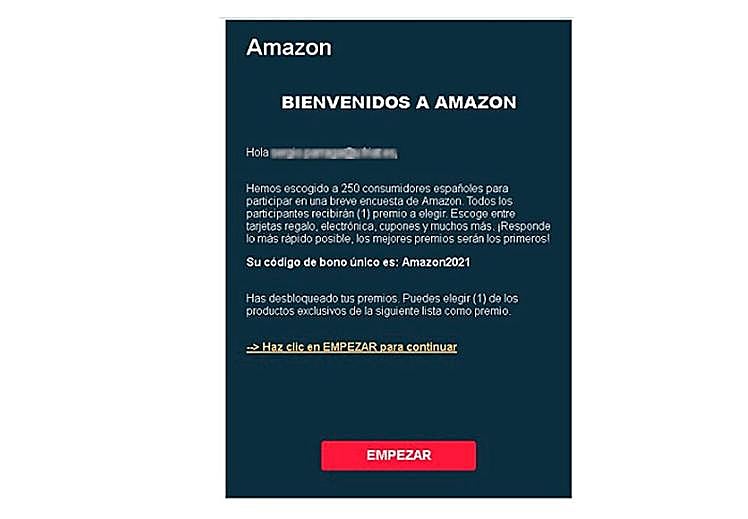
Amazon itself warns on its website: "From time to time, you may receive emails that appear to be sent by Amazon Pay, but are in fact fake. These emails may include links to a web page that looks similar to the Amazon Pay web page; you may even be asked to provide account information such as your email address and password."
These fake websites can be used to steal sensitive login or payment details, which are then used to commit fraud. Some phishing messages contain viruses or malware that can detect passwords or personal data.
Amazon makes it clear that it never asks customers to provide personal information by email, but only through the Amazon Pay website. Similarly, it never sends attachments.
Other warning signs are: grammatical or spelling errors in the email, a domain other than Amazon in the sender (such as msn.comn, hotmail.com or yahoo.com), a URL address that does not contain the Amazon Pay domains (pay.amazon.es, pay.amazon.com/es, payments.amazon.com/es, authorize.payments.amazon.com/es or eu.account.amazon.com). If in doubt, do not click on the link in the message, but go directly to the official website and log in to check your account information. "If you are unable to access your account or notice anything suspicious, please let us know immediately," Amazon says. And if you have clicked on the link and/or provided any information, you should change your passwords immediately and check for fraudulent activity. Sometimes cybercriminals adopt stealthy tactics to avoid leaving a trail, such as buying gift cards at the victim's expense.
12
The electricity company
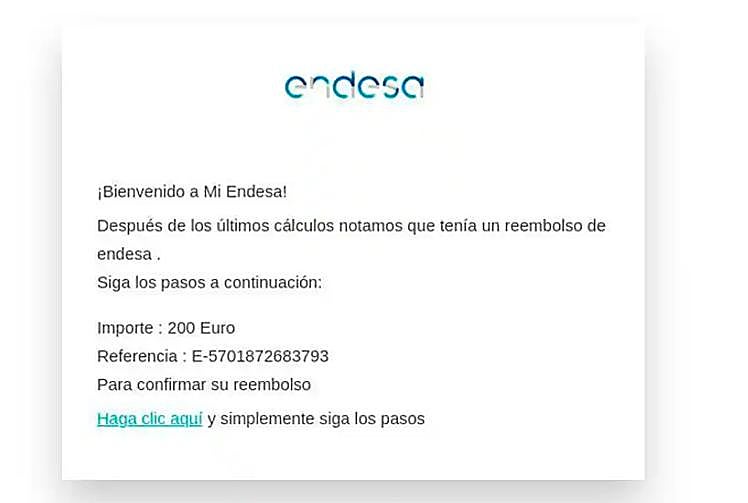
Zoom
Incibe has recently warned of an Endesa impersonation campaign, via fraudulent e-mails, in which the victim is informed of a supposed billing error for which a refund of 200 euros is to be made. To do this, they divert you to a website that claims to be the official Endesa customer area, where they will be asked for a series of personal data and data linked to the credit card (card number, expiry date, security code and PIN).
Endesa does not send this type of mail and if by any chance the user is waiting for a refund, they should go to their customer area on the company's website or telephone to check the status of the refund.
How to detect if an email or message is fraudulent
-Check spelling and wording: Many phishing messages contain spelling and grammatical errors due to the use of automatic translators.
-Verify that the email account is legitimate: We should check that the email address matches the organisation or company that is supposedly sending us the email. Scammers generally use public domains or domains that resemble the official email address (netflixx.com instead of netflix.com).
-If in doubt, check with the organisation or company by other means and confirm that they have actually sent you the email or message before replying.
-Check the URL of the links: Before clicking on a link, place the mouse cursor over the hypertext to see the address of the web page to which it redirects you.
-Be wary of shortened URLs, as it is not possible to check whether the destination is legitimate or not. Legitimate websites will not use them to ask you for data.
-Do not download attachments. Under no circumstances download attachments if you cannot confirm that it is a legitimate message.
-Before logging in to a website, check that it uses https://, but don't stop there: check its certificate details by clicking on the padlock in the browser bar.